- Understanding Networks - LAN, WAN, MAN with examples
- OSI Model - 7 Layers Explained with Analogies
- TCP/IP Model - 4 Layers and OSI Mapping
- Physical Layer - Cables, Hubs, Repeaters, Signals
- Data Link Layer - MAC Addresses, Switches, Ethernet Frames
- IP Addressing - IPv4 Structure and Octets
- Decimal to Binary Conversion
- Subnetting Fundamentals and CIDR Notation
- Calculating Network and Host Ranges
- IPv6 Addressing - Format and Purpose
- Public vs Private IP Addresses
- IPv4 vs IPv6 Comparison
- Common Protocols - HTTP, HTTPS, FTP, SSH, SMTP
- Port Numbers and Usage
- DNS Resolution Process
- DNS Records - A, MX, CNAME
- DHCP - Automatic IP Assignment
- Routing - Routers, Routing Tables, Default Gateways
- TCP vs UDP - Three-Way Handshake and Reliability
- nslookup and dig Commands
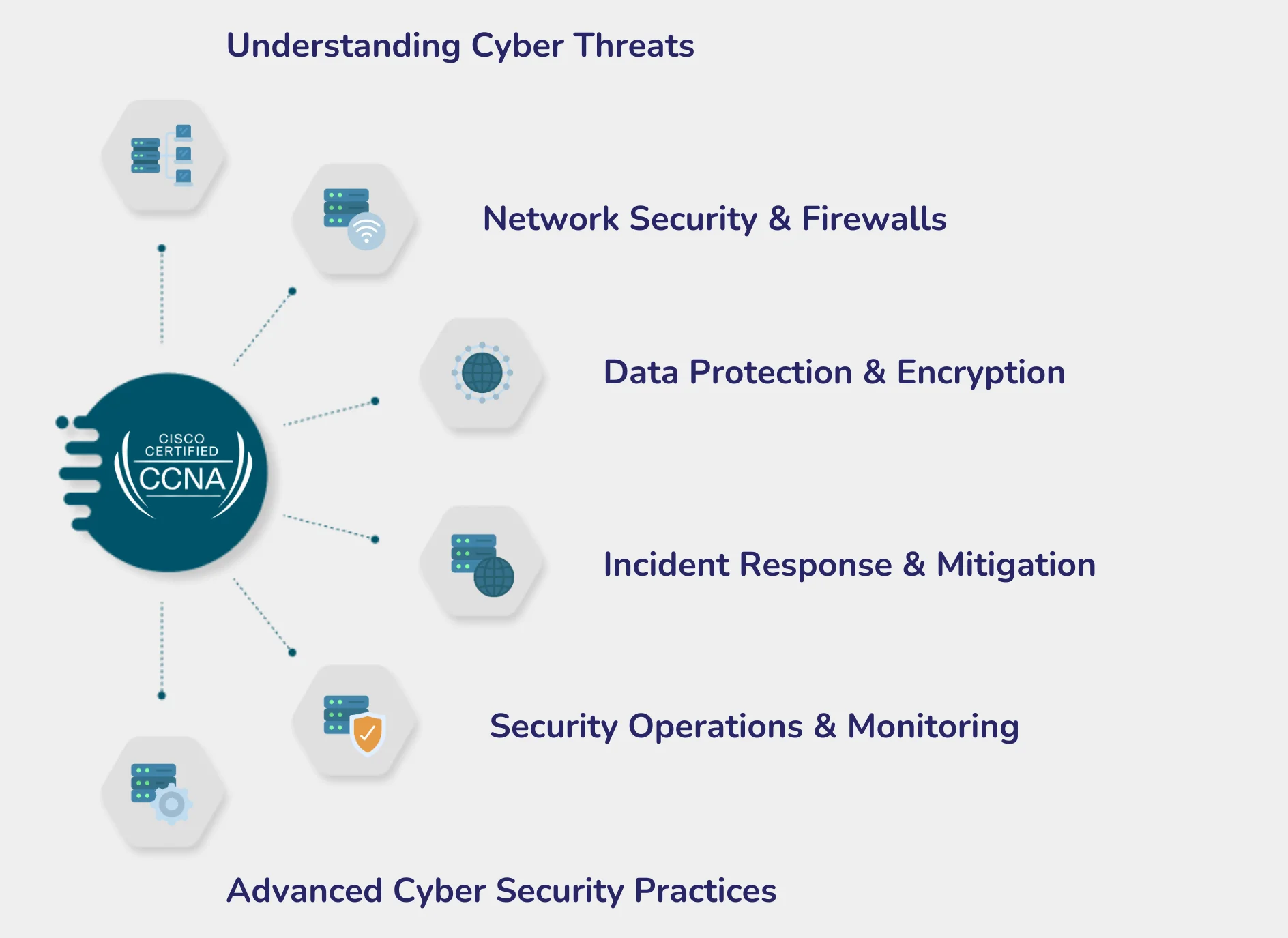
- Firewalls - Packet Filtering and Stateful Inspection
- VLANs - Segmentation, Trunk Ports, Tagging
- Wireless Networking - 802.11 Standards, WPA2/WPA3
- Wireshark - Packet Capture and Protocol Filtering
- Analyzing HTTP and DNS Transactions
- VirtualBox and Kali Linux Installation
- Linux Filesystem Structure - /, /home, /etc, /var, /bin, /usr
- Navigation Commands - pwd, ls, cd, tree
- File Operations - touch, mkdir, cp, mv, rm
- File Reading - cat, less, more, head, tail, pipes
- User Management - adduser, usermod, groupadd
- Permissions (rwx) and chmod
- Ownership - chown, chgrp
- sudo, Root Access and Privilege Escalation
- Process Management - ps, top, htop, kill
- Package Management - apt, dpkg
- Networking Commands - ifconfig, ip a, netstat, ss
- Text Processing - grep, awk, sed
- Bash Scripting - Variables, Conditionals, Loops
- Cron Jobs and Task Scheduling
- Log Files - /var/log, auth.log, journalctl
- CIA Triad - Confidentiality, Integrity, Availability
- Threat Actors - Script Kiddies, Hacktivists, Nation-States, Insiders
- Malware Types - Viruses, Worms, Trojans, Ransomware, Spyware
- Social Engineering - Phishing, Vishing, Smishing, Pretexting
- Password Attacks - Brute Force, Dictionary, Credential Stuffing
- Network Attacks - DoS, DDoS, MITM, ARP Spoofing
- Web Attacks - SQL Injection, XSS, CSRF
- Injection Attacks - Command Injection, LDAP Injection
- Cryptography Basics - Symmetric vs Asymmetric, AES, RSA
- Hashing - MD5, SHA-1, SHA-256 and Salting
- Analyzing Real Phishing Emails
- Layered Security Approach and Controls
- Zero Trust Architecture - Never Trust, Always Verify
- Public Key Infrastructure - CA, SSL/TLS, Digital Signatures
- Authentication - MFA, Biometric, Token, SSO
- Firewalls and IDS/IPS - Rules, Signatures, Anomalies
- SIEM Fundamentals - Logging, Event Correlation, Splunk Intro
- Incident Response - 6 Stages (Prepare to Lessons Learned)
- Vulnerability Management - Scanning, CVSS, Patching
- Risk Management - Likelihood x Impact, Risk Registry
- Cloud Security - Shared Responsibility, IAM, S3 Misconfigurations
- Endpoint Security - AV, EDR, Application Whitelisting
- Compliance - GDPR, PCI-DSS, Data Classification
- Hacking Mindset and Rules of Engagement
- Hacking Cycle - Recon, Scanning, Access, Maintaining, Clearing
- Passive Recon - WHOIS, Shodan, LinkedIn OSINT, Google Dorking
- Active Recon - Ping Sweep, Traceroute, Banner Grabbing
- Nmap - Scan Flags (-sS, -sV, -O)
- Enumeration - NetBIOS, SNMP, LDAP, SMB
- Vulnerability Scanning with Nessus
- Metasploit Framework - msfconsole, Payloads, Exploits
- Web Hacking Environment - DVWA, WebGoat
- SQL Injection - Manual Testing and sqlmap
- XSS Attacks - Reflected, Stored, DOM-Based
- Burp Suite - Interception and Parameter Tampering
- Directory Traversal and File Upload Vulnerabilities
- Password Cracking - Hashcat and John the Ripper
- ARP Poisoning with Ettercap (Lab)
- Session Hijacking and Cookie Stealing
- Wireless Attacks - WPA2 Handshake with aircrack-ng
- IDS Evasion Techniques
- Social Engineering Toolkit (SET) - Phishing Pages
- AI & ML Basics for Security - Supervised, Unsupervised, Reinforcement Learning
- AI-Powered Attacks - Automation and AI-Generated Phishing
- Deepfake Attacks - Voice Cloning and Face Swapping
- AI-Enabled Malware - Polymorphic Malware
- Adversarial Machine Learning - Tricking Models
- Deepfake Detection Tools and Limitations
- AI-Based Anomaly Detection and UEBA
- AI in Intrusion Detection vs Signature-Based IDS
- AI in SIEM - Alert Management and Noise Reduction
- AI in Threat Intelligence - IOC Correlation
- AI-Driven Vulnerability Prioritization
- Microsoft Sentinel and AWS GuardDuty (Free Tier)
- ChatGPT / Claude in Penetration Testing
- AI-Generated Exploits, Reports, and Scripts
- AI-Powered OSINT and Automated Reconnaissance
- Prompt Injection Attacks on LLMs
- AI-Based Code Review for Vulnerabilities
- Automating Pentest Reports with AI
- AI-Assisted Recon on Bug Bounty Targets (HackerOne)
- AI Ethics and Responsible Use in Security
- Cloud Security - AI-Based Misconfiguration Detection
- IoT Security - AI Anomaly Monitoring
- Portfolio Building - GitHub, Writeups, Blog Posts
- Capstone - End-to-End Pentest on TryHackMe CTF
- Capstone - Professional Report with AI Tools